Introduction
Device binding is commonly used in android application for tracking a user’s device and ensure accountability. Some android application developers use this device id binding technique to uniquely identify users. When an application offers the discount promo code for user’s benefits, application acquires device attribute to track users against that specific promo code. In some case, the developer uses IMEI number to validate the user’s applied promo code whether it is valid or not.
Following are the device attributes used by an android application for device id mapping.
- Android device ID
- IMEI no.
- Mac address
Below is a scenario in which by changing IMEI number, device id binding validation is bypassed. IMEI number is a unique for each mobile handset, used by GSM to identify a valid device on the network.
Pre-requisites
- A rooted Android device
- Xposed framework
- IMEI changer pro application
IMEI number validation bypass
This scenario is based on android application which uses the IMEI number for device ID mapping. The business purpose of the application was to provide a promotional offer on a new application installation and for a new user ID. Hence a user cannot avail the same offer if any of below cases:
- If the user ID was registered on any of the device.
- If the mobile application was previously installed on the device. (uninstalling and reinstalling the application, then promo code won’t work to avail any offer)
Hence to avail the offer, an unregistered user should download the application to the mobile devices for the first time.
[Validation] Note: Application provides the user to generate a pin for accessing some good offers on ecommerce application. Only onetime, a single user with an android device can register for pin generation after a successful generation of pin user cannot register again. Application sends all parameter in encrypted form and it has also a request checksum to validate the request integrity.
Steps to bypass the IMEI validation
Firstly, attacker registers himself on a valid android device. After that his device maps with his corresponding user id and he generates the pin.
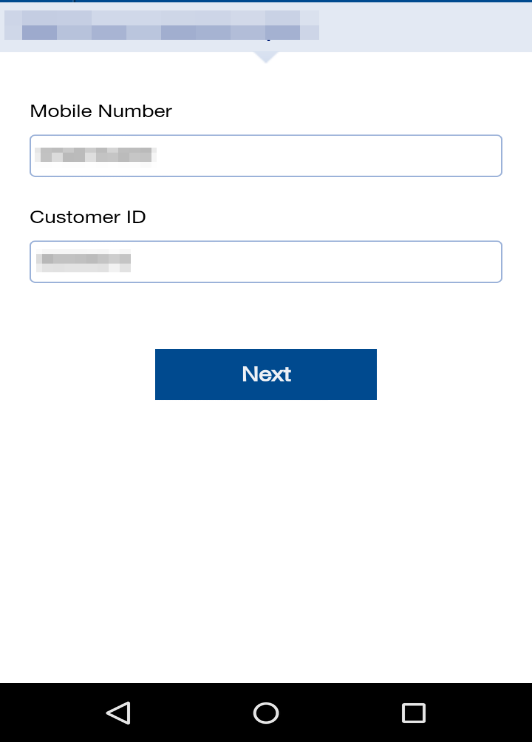
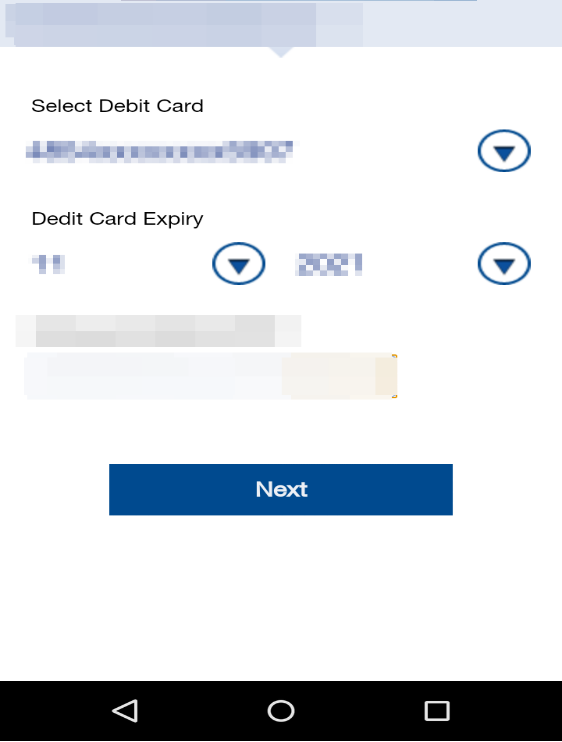
After registration, attacker again enters all the details for generating pin as shown in figure 1.
After submitting the request, application throws an error that the “Device is already registered with another CustID”
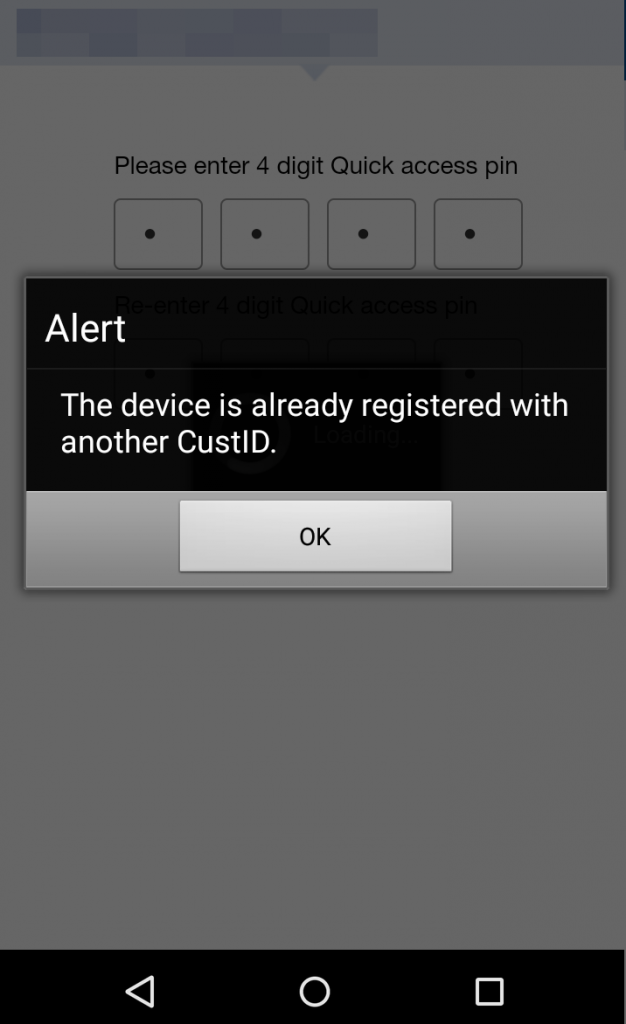
It was observed that application is using IMEI number mapping when user register by submitting his first pin generate request.
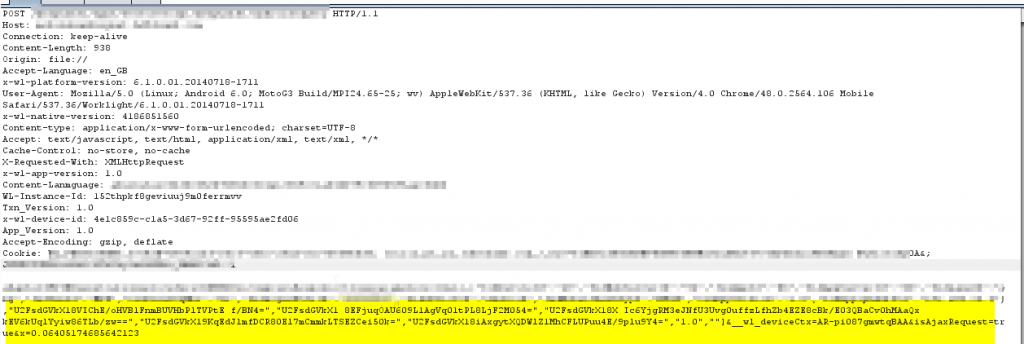
After analyzing the burp request of pin generation, it was observed that application’s whole request was in encrypted form. So it would be difficult for an attacker to tamper the parameter values of IMEI number as shown in figure 4.
Changing IMEI number through Xposed framework
To change IMEI number attacker should have a root android device. Xposed IMEI changer is an android application which helps to change IMEI number for other applications. It is a module under Xposed framework, it doesn’t change the IMEI number permanently but it changes the IMEI number virtually to fool other application.
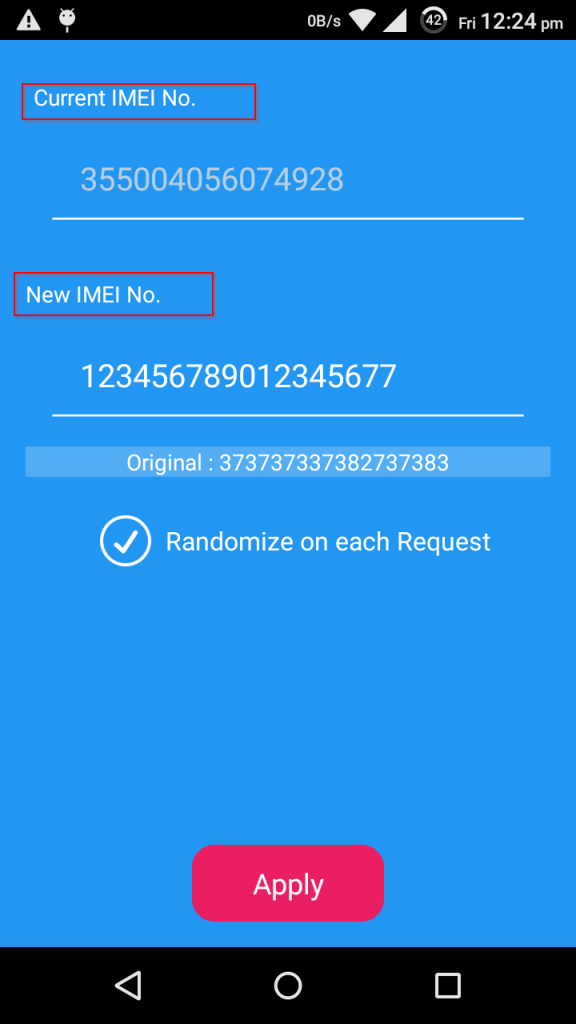
After changing the IMEI number, attacker can generate Pin for promo offer successfully as shown in figure Below.
Recommendation
- Device binding for application should not rely on single value attribute of device. Developer may use such as App ID, Android device id, MAC address.
- It is recommended to use random token with IMEI no and other attributes of device.
- Application must use hashing algorithm when it sends to server side for validation of device.
- Application must have root detection capabilities, after that it would be difficult to change device attributes such as IMEI, android id and app ID for an android device user.
- Application preference file contents should be in encrypted or unreadable form.
Rajesh Kumar is Working as an Information Security Analyst at Network Intelligence (I) Pvt. Ltd. His work mainly focuses on Vulnerability Assessment and Penetration Testing for NII’s premier clients. However his specialization is mobile application security, web application security and research.
This is really cool. Keep it up Rajesh !!
Thanks for reading, Abhijit.
Good one
Very Helpful Information , Thanks !
Hello ,
Its a nice article .
But what if device is not compatible for xposed framework?
or xposed framework is not supported?
Nice information, Thanks for sharing your info.